Check the Management Roles Assigned to You and Try Again
Exchange Server uses a permissions model called Role Based Access Control (RBAC) to manage the delegation of permissions for Exchange administrative tasks. RBAC was offset introduced in Exchange 2010 and continues to exist used in Exchange Server and Exchange Online today. It's of import to understand how RBAC works because it is the mechanism that you use to utilize a least-privilege approach to Exchange authoritative permissions. RBAC is also how stop users are granted permissions to perform tasks such as managing their own distribution groups.
In this tutorial we'll look at:
- How RBAC works past examining the pre-divers RBAC management roles
- How to configure custom management roles
The Nuts of Role Based Access Control
Whether you sympathise the inner workings of RBAC or non, y'all're still making use of information technology every day when you perform Exchange administrative tasks. That'southward because RBAC has a series of pre-divers management part groups, management roles, and direction role assignments for a variety of mutual administrative scenarios.
Management part groups are the security groups in Agile Directory. Y'all tin see the direction office groups that Substitution creates during setup in the Microsoft Exchange Security Groups OU in Active Directory.
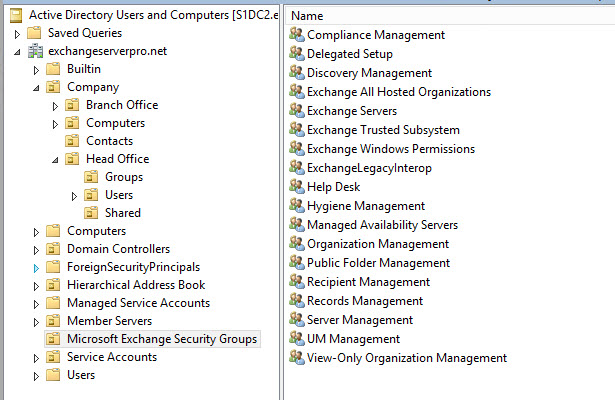
Some of those groups should already expect familiar to you, such every bit Organisation Management and Recipient Management. Some of the groups in that OU are for other purposes, such as the Substitution Trusted Subsystem group which contains reckoner accounts for Substitution servers. And then if you desire to see simply the role groups, you can switch to the Exchange Management Beat instead and run the Get-RoleGroup cmdlet.
| [ PS ] C : \ & gt ; Get - RoleGroup Name AssignedRoles RoleAssignments -- -- -- -- -- -- -- -- - -- -- -- -- -- -- -- - Organization Management { MyDiagnostics , MyContactI . . . { MyDiagnostics - Organizatio . . . Public Folder Management { Public Folders , Postal service Enab . . . { Public Folders - Public Fol . . . Recipient Direction { Move Mailboxes , Message T . . . { Move Mailboxes - Recipient . . . View - Simply System Homo . . . { View - Simply Configuration , . . . { View - Just Configuration - V . . . UM Direction { UM Prompts , Unified Messa . . . { UM Prompts - UM Direction , . . . Help Desk-bound { User Options , View - Simply R . . . { User Options - Assistance Desk , V . . . Records Direction { Transport Rules , Audit Lo . . . { Transport Rules - Records M . . . Discovery Management { Mailbox Search , Legal Hold } { Mailbox Search - Discovery . . . Server Management { Monitoring , Exchange Serv . . . { Monitoring - Server Managem . . . Delegated Setup { View - Only Configuration } { View - Only Configuration - D . . . Hygiene Management { ApplicationImpersonation , . . . { ApplicationImpersonation - . . . Compliance Management { Data Loss Prevention } { Data Loss Prevention - Comp . . . |
Notice how each office group has one or more than assigned roles, which refer to direction roles. An example of a management role is Mail Recipients.
| [ PS ] C : \ & gt ; Get - ManagementRole "Post Recipients" Proper noun RoleType -- -- -- -- -- -- Mail service Recipients MailRecipients |
Management roles are collections of direction role entries. Direction role entries are specific tasks that tin be performed by users who are assigned with that particular role. Standing with the example of the Mail Recipients role, the direction part entries tin can exist summarized by looking at the description of the management function.
| [ PS ] C : \ & gt ; Get - ManagementRole "Mail service Recipients" | fl Description This role enables administrators to manage existing mailboxes , mail users , and mail contacts in an organization . This function tin can 't create these recipients. Use MailRecipientCreation roles to create them. This part type doesn' t enable yous to manage mail - enabled public folders or distribution groups . Use the MailEnabledPublicFolders and DistributionGroup roles to manage these objects . If your organisation has a split permissions model where recipient cosmos and management are performed by different groups , assign the MailRecipientCreation roles to the grouping that performs recipient creation and the MailRecipients roles to the group that performs recipient management . |
And so the Post Recipients part contains a whole bunch of role entries to make that possible. Role entries accept a naming convention of "RoleEntry", so all of the office entries for the Mail Recipients role will exist named "Mail service RecipientsEntry". This means that you can see the list of role entries for the Post Recipients function by running the post-obit command:
| [ PS ] C : \ & gt ; Get - ManagementRoleEntry "Mail service Recipients*" | Select Proper noun |
On my system there'southward 125 role entries for the Mail Recipients part, so I won't listing them all hither. Just they basically include all the cmdlets y'all'd demand for that purpose, such equally Become-Mailbox, Set-Mailbox, and Enable-Mailbox (for post-enabling an existing user). Nonetheless, information technology is a separate direction role called "Mail service Recipient Creation" that has the role entries that permit creating entirely new recipients, such as New-Mailbox, New-MailUser, and New-MailContact.
Both the Post Recipients and Post Recipient Creation roles, along with others, are assigned to the role group named Recipient Management. Y'all can see the function assignments for the Recipient Management role group by running the Get-RoleGroup cmdlet.
| [ PS ] C : \ & gt ; Become - RoleGroup "Recipient Management" | Select - ExpandProperty Roles | Select Name Name -- -- Movement Mailboxes Message Tracking Mail Recipient Creation Post Recipients Mail Enabled Public Folders Recipient Policies Migration Distribution Groups Team Mailboxes |
The Recipient Management role group is one of the Active Directory security groups that exists in the Microsoft Exchange Security Groups OU. Therefore, if you add a user account to the Recipient Direction group, they are granted the ability to perform those administration tasks such as managing postal service recipients, distribution groups, and performing message tracking. When that user opens the Commutation Management Shell, but the cmdlets that are included in the role entries for the direction roles assigned to the office groups they are a fellow member of volition exist available. For example, a Recipient Management role group member won't accept admission to the New-AcceptedDomain or Ready-AcceptedDomain cmdlets, but they practice take access to the Get-AcceptedDomain cmdlet.
When the user logs into the Exchange Admin Center, they will also come across only the sections that they have access to through their role group membership. For case in the screenshot below, the web browser on the left shows the sections visible to a Recipient Management role group member, and the browser on the correct shows the sections visible to an Arrangement Management function group member.
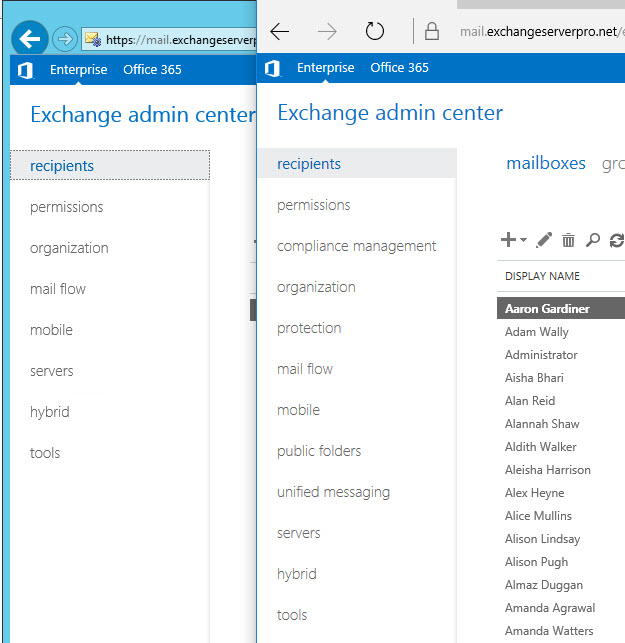
Some of the differences are obvious, for example the Recipient Management role group member can't see the compliance direction section of the Exchange Admin Heart. Others are not so obvious at offset. Both users tin encounter the mail menstruation department where things like Accepted Domains are managed. The Recipient Direction part group holder can still see that department, because they need to be able to "see" the list of accustomed domains in the organisation when assigning SMTP addresses to recipients. But they tin can't edit whatsoever of the accepted domains, nor tin they add new ones.
As the final piece of the RBAC pic, in that location's likewise the concept of management role scope. The direction roles (such as Mail Recipients) assigned to the pre-canned office groups (such equally Recipient Direction) accept a scope of "Organization", which effectively means they employ to the entire organization. Management roles tin can be scoped to more specific area, such equally to a unmarried organizational unit in Active Directory.
So to summarize what's been covered then far, RBAC is fabricated up of:
- Direction part entries, which are specific tasks that a user can perform, such as running the Set-Mailbox cmdlet.
- Direction roles, which are collections of role entries, such every bit the Mail Recipients role.
- Management office telescopic, which defines where in the system a management role is applicable to, such as the unabridged organization, a specific server, or a specific organizational unit.
- Management role assignments, which link management roles to function groups.
- Management role groups, which are security groups that users tin exist added to as members to grant them the permissions to perform administrative tasks.
In one case you are comfortable with those nuts, you lot can first looking at creating custom roles.
Creating a Custom RBAC Role
Permit's say that you have a user in the organization who is responsible for managing mail service contacts. To provide them with the permissions to perform that task, without whatsoever additional endeavor on your part, you would need to add them to the Recipient Management role group. Yet, that role group permits them to do much more just manage the mail service contacts they are responsible for, and so it doesn't marshal with the least privilege approach to security.
The more sensible approach is to create a custom RBAC part and assign it to that user, or to a part group that the user can be made a fellow member of.
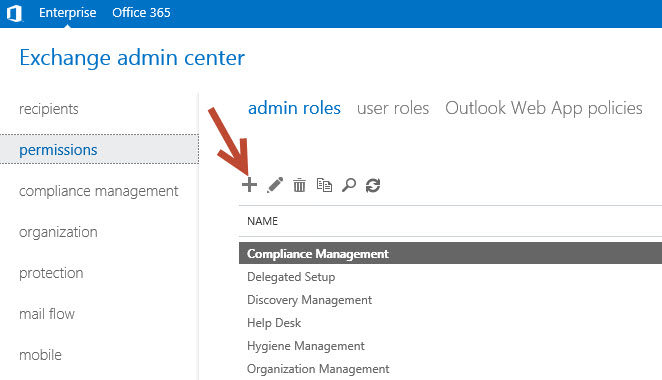
The easiest way to create a custom role is by using the Commutation Admin Center. In the permissions section under admin roles, click the icon to create a new role group.
Requite the role group a meaningful proper noun, and ready the organizational unit of measurement that you want to limit the role group to.
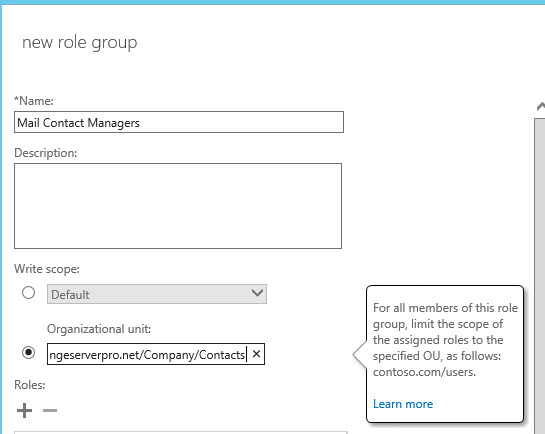
Next, click the icon to add a role. In scanning through the list of existing roles (remember, these are collections of role entries), there doesn't appear to be i already created for managing mail contacts. So a custom role (or 2) with the function entries for managing contacts needs to exist created. Creating custom roles is easiest when yous create the custom role based on an existing function, and and so customize information technology for your needs. In this example, Mail Recipients and Post Recipient Cosmos are the ii roles to base the new custom roles on.
| [ PS ] C : \ > New - ManagementRole - Parent "Post Recipients" - Name "Custom Role - Post Contacts" Name RoleType -- -- -- -- -- -- Custom Office - Mail Contacts MailRecipients [ PS ] C : \ > New - ManagementRole - Parent "Mail Recipient Creation" - Proper noun "Custom Role - Mail Contacts Creation" Name RoleType -- -- -- -- -- -- Custom Role - Mail service Contacts Creation MailRecipientCreation |
The next pace is to remove the unwanted role entries from each of the custom roles, and so that they're but left with the adequacy to manage post contacts.
| [ PS ] C : \ > Get - ManagementRoleEntry "Custom Function - Postal service Contacts\*" | Where { $ _ . Name - notlike "*MailContact" } | Remove - ManagementRoleEntry [ PS ] C : \ > Become - ManagementRoleEntry "Custom Office - Mail Contacts Cosmos\*" | Where { $ _ . Proper name - notlike "*MailContact" } | Remove - ManagementRoleEntry |
So now nosotros're left with two custom roles called "Custom Part – Mail Contacts" and "Custom Office – Mail Contacts Cosmos", each containing only the function entries required for managing contacts.
| [ PS ] C : \ > Get - ManagementRoleEntry "Custom Function - Mail service Contacts\*" Name Role Parameters -- -- -- -- -- -- -- -- -- Disable - MailContact Custom Role - Mail service Con . . . { Confirm , Debug , DomainController , ErrorAction , ErrorVariab . . . Enable - MailContact Custom Function - Postal service Con . . . { Alias , Ostend , Debug , DisplayName , DomainController , Erro . . . Go - MailContact Custom Role - Mail Con . . . { Anr , Credential , Debug , DomainController , ErrorAction , Err . . . Set - MailContact Custom Part - Mail Con . . . { AcceptMessagesOnlyFrom , AcceptMessagesOnlyFromDLMembers , A . . . [ PS ] C : \ > Go - ManagementRoleEntry "Custom Office - Mail service Contacts Creation\*" Name Role Parameters -- -- -- -- -- -- -- -- -- Become - MailContact Custom Role - Mail Con . . . { Anr , Credential , Debug , DomainController , ErrorAction , Err . . . New - MailContact Custom Function - Mail Con . . . { Allonym , ArbitrationMailbox , Ostend , Debug , DisplayName , Do . . . Remove - MailContact Custom Role - Mail service Con . . . { Confirm , Debug , DomainController , ErrorAction , ErrorVariab . . . |
With a slightly unlike approach y'all could also create one single custom function containing all of the role entries you need, instead of two custom roles. Just this approach of creating custom roles based of existing roles is a nice, easy mode to do the task.
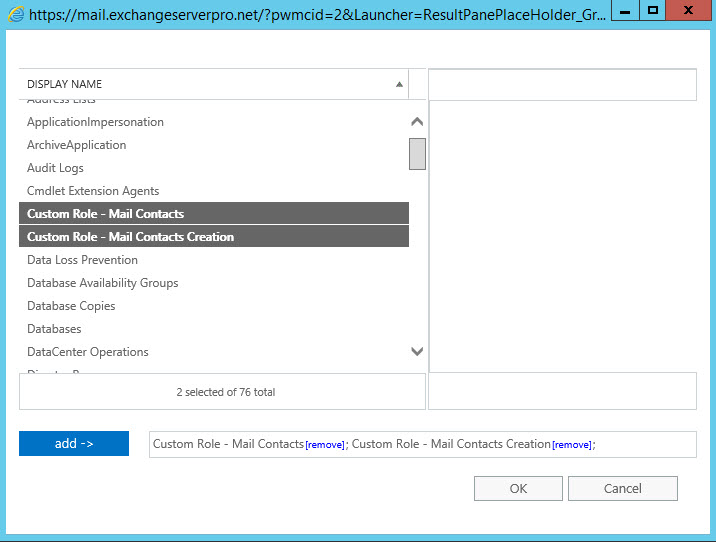
Dorsum to the Exchange Admin Center, the two custom roles are now visible in the picker to add together to the new function group we're creating. Add the two custom roles, and also add the View-Only Recipients role.
Finally, add the users who volition be performing the administrative tasks to the role group as members, and save the new role group.
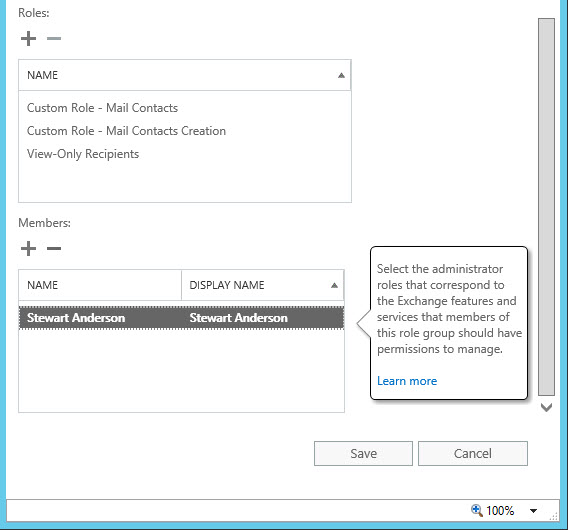
When the members of the new "Postal service Contact Managers" role group log in to the Exchange Admin Center, they'll be able to see the recipients in the organization (just as they tin see them in the global address list via Outlook), and in the Contacts area will be able to create new Mail service Contacts. If the role group fellow member shown above tries to create a contact in an OU other than the i their role has been scoped to, they'll receive an error.
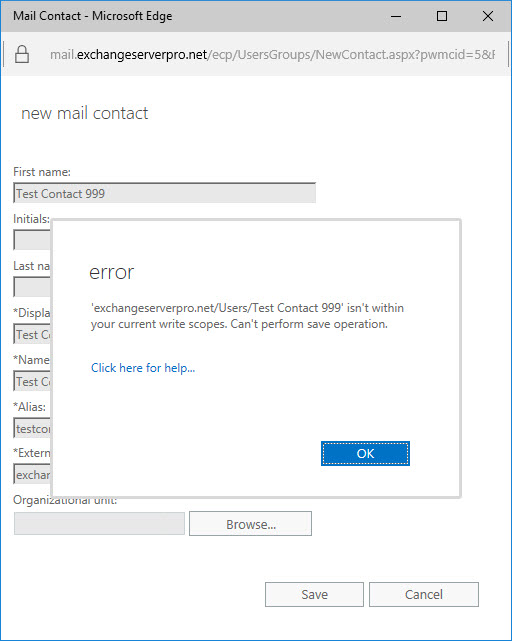
Only if they cull the right OU when creating the contact, they'll exist successful. The same OU restrictions likewise apply to modifying or deleting contacts.
Summary
In this tutorial I've demonstrated how to employ pre-divers management roles in Commutation Server to assign RBAC permissions for administrative tasks. I've also demonstrated how to create custom roles and role groups to assign limited permissions to users for specific tasks.
andersonreame1974.blogspot.com
Source: https://practical365.com/exchange-server-role-based-access-control-in-action/
0 Response to "Check the Management Roles Assigned to You and Try Again"
Post a Comment